Cyber criminals can target more than one person at a time. In 2017 ransomware was under the spotlight with the WannaCry and NotPetya attacks which temporarily paralyzed many large companies.

Why Malaysia Should Amend Its Cyber Security Laws
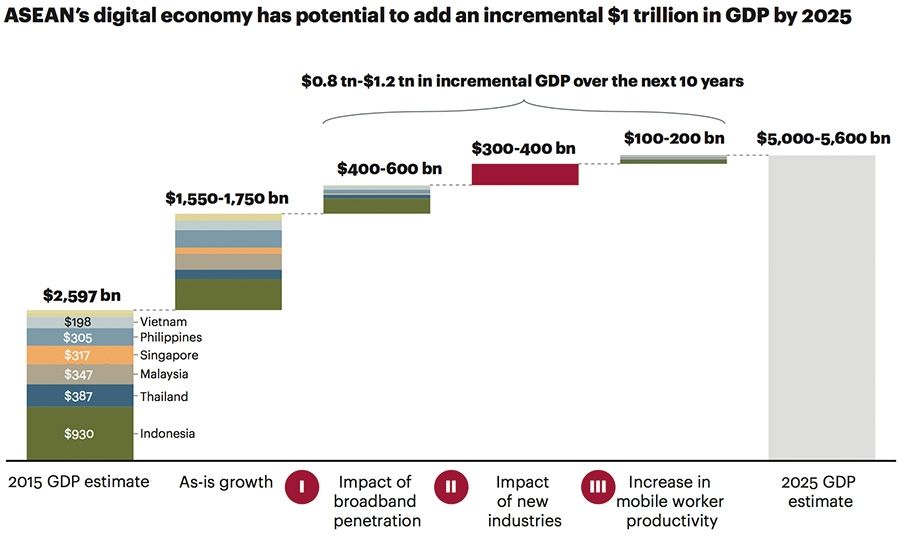
Asean Needs Cohesive Approach To Cybersecurity To Reach Its Full Digital Potential

Cybersecurity Industry Report Investment Case Nasdaq
A case which had been NFA-ed in 2018.

Cyber attack in malaysia 2018. With attackers adopting and deploying increasingly advanced and sophisticated tools and organisations struggling to address cybersecurity challenges - not least talent and skill shortages - if not when is. Besides victims of cyberbullying are two times more likely to attempt suicide. Why 310 of Robinhoods 7 Million Cyber-Attack Victims Should Be Really Quite Worried Vlad Savov Bloomberg News The Robinhood application is displayed in the App Store on an Apple Inc.
In latest cyber attack. LineStar Integrity Services a pipeline-focused business was hit by a ransomware attack the same time as the Colonial Pipeline with 70 gigabytes of. One of the biggest cyber-espionage cases in recent times was the massive supply chain attack on SolarWinds.
The Digital and Cyberspace Policy programs cyber operations tracker is a database of the publicly known state-sponsored incidents that have occurred since 2005. AppleJeus has been used by Lazarus Group targeting companies in the energy finance government industry technology and telecommunications sectors and several countries including the United States United Kingdom South Korea Australia Brazil New Zealand and Russia. IPhone in an arranged photograph taken in Washington DC US on Friday Dec.
And the BSIA CCTV section recently urged operators of IP-connected surveillance systems to do more to safeguard their systems against cyber attack including changing the manufacturers default credentials. The process also depends on the position for which the hiring is done. AppleJeus is a family of downloaders initially discovered in 2018 embedded within trojanized cryptocurrency applications.
No wonder the cyber threat to CCTV systems has been in the news a lot recently. Security Magazine and Infosecurity Magazine. Last week around 15m IoT devices mostly security cameras were hijacked during a DDoS attack.
Toronto police say in a release that. The survey was conducted by Ipsos - an international market research company - and it involved 20793 respondents worldwide in 2018. On a positive note recognition of the need to improve cyber-defenses appears to be growing with 93 of businesses allocating a special budget to fight ransomware threats.
What is the Cyber Kill Chain Model. M-Trends is an annual publication from FireEye and Mandiant with timely data and insights based on frontline investigations of high-impact cyber attacks and remediations. The disruption happened when a backup system failed to kick in after a hardware malfunction according to the Japan Exchange Group.
Also in 2018 18 of young people reported self-harming at least once after being harassed online. The availability of virtual spaces to public and private sectors has allowed cybercrime to become an everyday occurrence. In 2016 758 million malicious attacks occurred according to KasperskyLab an attack launched every 40 seconds and the cost of cybercrime damages is expected to hit 5 trillion by 2020.
Cyber Issues Economic Prosperity and Trade Policy Energy Global Health Global Womens Issues Human Rights and Democracy Human Trafficking The Ocean and Polar Affairs Refugee and Humanitarian Assistance Science Technology and Innovation Treaties and International Agreements. The Cyber Security graduate certificate program at George Brown College is designed to meet the high demand for cyber security professionals and related IT security professionals across multiple sectors including consulting services finance and health care. Similar in concept to the militarys model it defines the steps used by cyber attackers in todays cyber-based attacks.
M-Trends Reports M-Trends 2021 Insights into Todays Top Cyber Trends and Attacks. In addition 29 of parents said that their children were depressed for a time after a cyberbullying attack. According to CNN reports Russian hackers who were behind the 2020 breach of US federal agencies continue to try and infiltrate US and European government networks.
In 2011 Lockheed Martin released a paper defining a Cyber Kill Chain. The number of cyber attacks has grown up steadily over the last few years. The halt wasnt connected to a cyber attack.
When compared to only Asian countries Malaysia ranked second behind India which was placed first on the list. KUALA LUMPUR 9 January 2020 - Cybersecurity practitioners have for many years been promoting the adage its not if but when organisations will be impacted by a cyber attack. Cybersecurity Laws and Regulations 2022.
On October 1 2020 a technical glitch halted trading on Japans stock exchanges including the Nikkei 225. Sarawak Report editor Clare Rewcastle Brown says the police should focus on crooks who are stealing from Malaysia. The UKs Foreign and Commonwealth Office as well as security.
Top 50 Cyber Security Interview Questions and Answers updated for 2018 The interview process is tough not only for the candidates but also for the interviewers. TORONTO Police say a woman who was severely hurt in the 2018 Toronto van attack has died of her injuries in hospital. In 2018 The Internet Crime Complaint Center received 351937 complaints of cybercrime which lead to 27 billion lost.
Cyber Security Penetration Testing Firm. Established in 2005 LGMS is accredited with multiple international certifications that makes it a leading cyber security penetration testing and assessment firm in the Asia Pacific region. Alarmingly around one-third attributed a ransomware attack as the cause for employee layoffs.
Operation Pawn Storm 2014 EFF spoof - White House and NATO attack 2015 Breach of Democratic National Committee 2016 World Anti-Doping Agency attack 2016 Attack on Dutch ministries 2017 IAAF Hack 2017 German elections 2017 Breach of the International Olympic Committee 2018 Olympic Destroyer 2018 US. Kill chain is a term originally used by the military to define the steps an enemy uses to attack a target. Booz Allen Hamilton is spinning out SnapAttack a commercial cybersecurity product shop it created but Booz Allen will primary channel for federal customers looking to.
The attack occurred during the countrys investigation of the Malaysia Airlines Flight 17 MH17 that was shot down in 2014. ICLG - Cybersecurity covers common issues in cybersecurity laws and regulations including cybercrime applicable laws preventing attacks specific sectors corporate governance litigation insurance and investigatory and police powers in 23 jurisdictions. Fancy Bear also known as APT28 by Mandiant Pawn Storm Sofacy Group by Kaspersky Sednit Tsar Team by FireEye and STRONTIUM by Microsoft is a Russian cyber espionage group.
Cybersecurity firm CrowdStrike has said with a medium level of confidence that it is associated with the Russian military intelligence agency GRU. LGMS is named as one of the Internet of Things IoT key penetration testing vendors in the 2018 IDC Report.
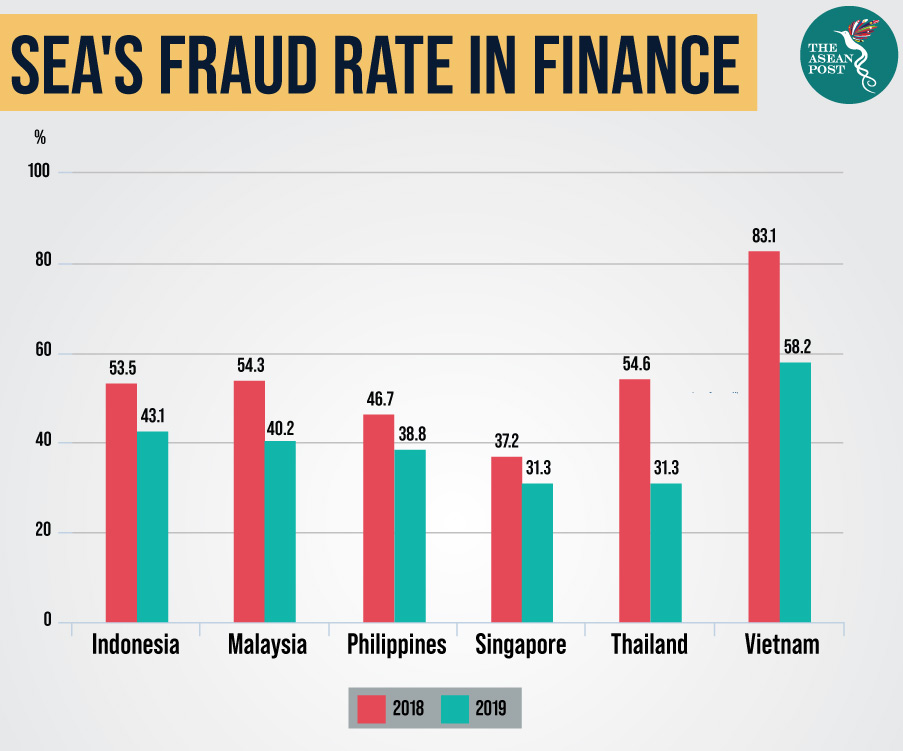
Digital Fraud On The Rise In Asean The Asean Post

Cybersecurity Threats To Cost Organizations In Asia Pacific Us 1 75 Trillion In Economic Losses Microsoft Stories Asia
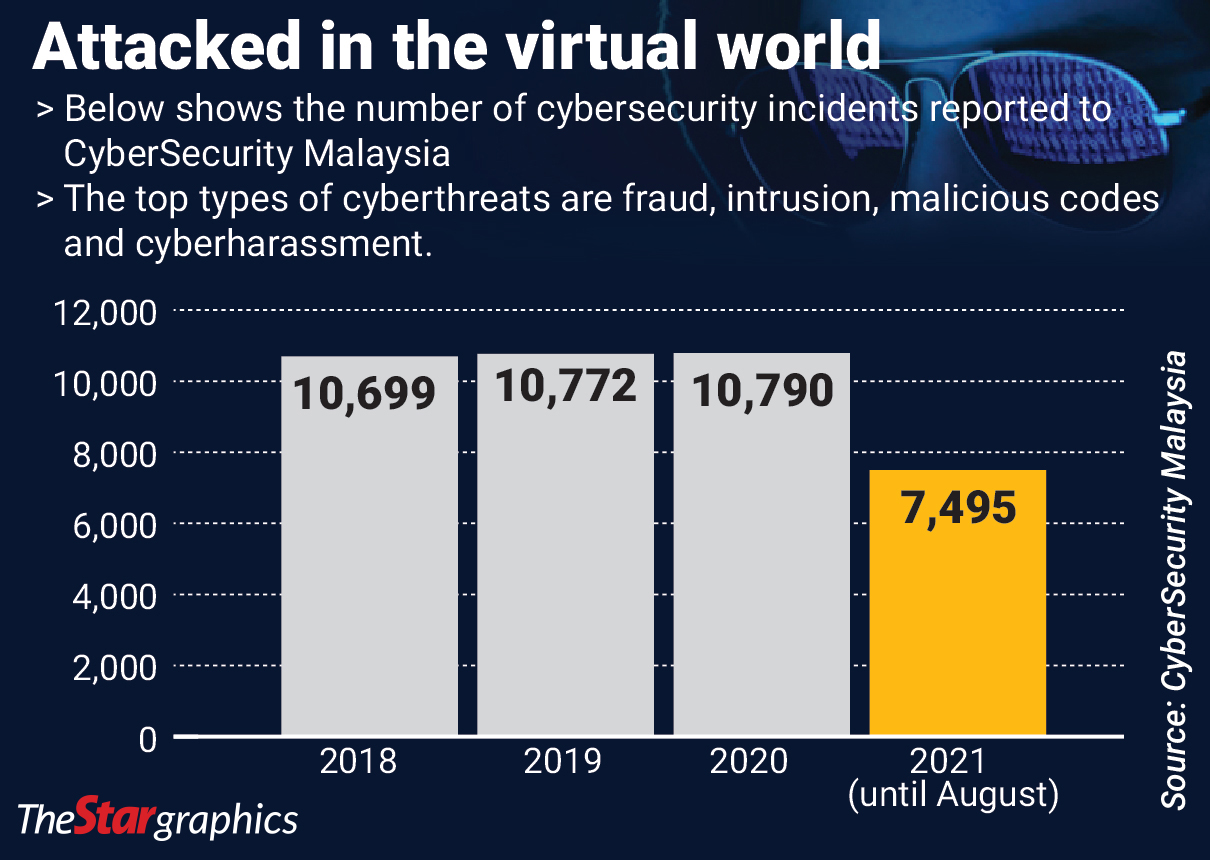
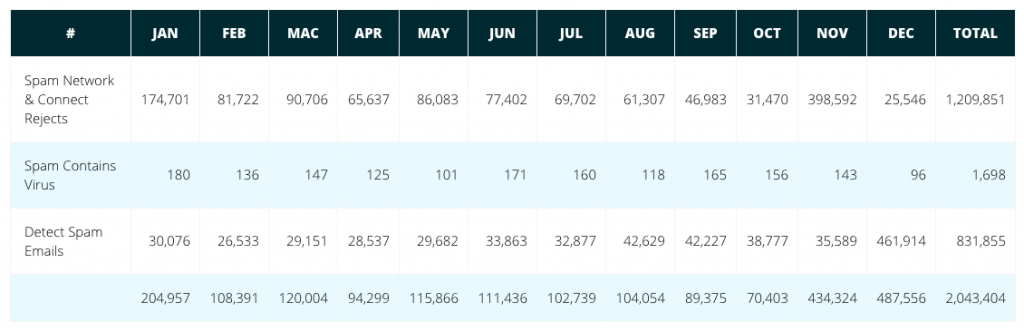
Online Threats Continue To Spike The Star
2
Why Malaysia Should Amend Its Cyber Security Laws
Cybersecurity Cases Rise By 82 5 The Star

The Great Data Robbery
Facts Statistics Identity Theft And Cybercrime Iii

